The rules of credential fraud have changed.
In 2023, creating a fake certificate required Photoshop skills, time, and luck. In 2026, anyone with internet access can generate a convincing fake credential in under five minutes using freely available AI tools.
Template replication: AI analyses legitimate credentials and generates pixel-perfect reproductions — correct fonts, logos, layouts, paper textures.
Image generation: AI creates authentic-looking signatures, seals, and security features that would cost fraudsters thousands in equipment to physically produce.
Content variation: AI generates unique details — names, dates, programme titles, registration numbers — that appear consistent and legitimate.
Quality at scale: AI produces hundreds of fake credentials faster than any human could create one. Industrial-scale fraud becomes trivially easy.
Traditional credential security followed a pattern: issuers added security features, fraudsters learned to replicate them, issuers added more features.
Watermarks. Holograms. UV printing. Embossed seals. Each innovation bought time until counterfeiters caught up.
AI breaks this cycle. When AI can replicate any visual element, visual security features become meaningless. The arms race is over — and detection lost.
The question isn't whether AI-generated credential fraud will affect your organisation — it's whether you'll be protected when it does.
Every traditional credential security measure shares a fatal flaw: they're based on making credentials difficult to replicate visually. AI eliminates that difficulty.
Holograms: AI image generators can create holographic effects indistinguishable from real holograms in photographs and videos.
Watermarks: AI trivially replicates watermark patterns from sample images.
Security printing: Microtext, guilloche patterns, and rainbow printing can all be generated synthetically.
Embossing: 3D rendering produces images that appear embossed. Physical fraud just requires a cheap embossing stamp.
Signatures: AI generates handwritten signatures that pass visual inspection.
"Just verify against our database" sounds simple until you consider:
Training humans to detect AI-generated fakes requires constant updates as AI capabilities improve. The cognitive load of inspecting every credential for AI tells exceeds human capacity at scale.
Even skilled forensic examiners cannot reliably distinguish advanced AI-generated credentials from originals. When detection accuracy drops below 70%, the process becomes security theatre.
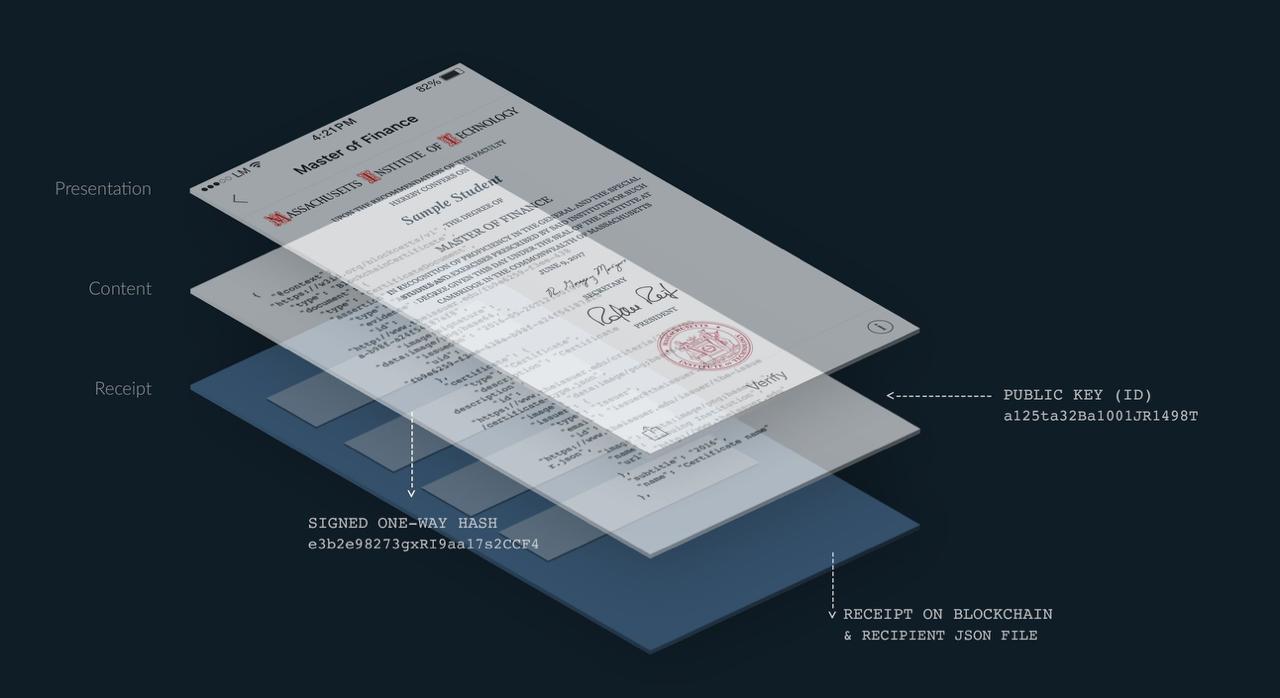
Blockchain verification doesn't try to detect fakes. It proves authenticity from the moment of issuance — a fundamentally different approach that AI cannot circumvent.
Traditional security: Make credentials hard to copy → try to detect copies.
Blockchain security: Make credentials mathematically verifiable → copies fail verification automatically.
This isn't an incremental improvement. It's a complete change in security model.
Step 1: Credential Creation When your organisation issues a credential, TRUE creates a cryptographic hash — a unique digital fingerprint — of the credential's contents.
Step 2: Blockchain Recording This hash is permanently written to one or more public blockchains (Ethereum, Polygon, AVAX, Fantom). The record is immutable — it cannot be changed or deleted.
Step 3: Verification When anyone needs to verify the credential, the system:
No visual analysis required: Verification is mathematical, not visual. It doesn't matter how convincing a fake looks — it fails verification because the hash doesn't match.
Unforgeable hashes: SHA-256 cryptographic hashing produces unique fingerprints. The probability of two different credentials producing the same hash is 1 in 2^256 — effectively impossible.
Decentralised proof: The blockchain record exists across thousands of computers worldwide. There's no single system to hack, no database to compromise, no point of failure.
Immutable history: Once recorded, the blockchain entry cannot be modified. Not by the issuer. Not by the recipient. Not by hackers. Not by anyone.
Permanent verification: The blockchain record survives even if your organisation closes. Credentials issued in 2026 will be verifiable in 2050 and beyond.
For the security-conscious reader, here's exactly why blockchain verification defeats AI-generated fakes:
SHA-256, the hashing algorithm used in blockchain verification, provides:
Determinism: The same input always produces the same output. A genuine credential's hash is predictable and repeatable.
Collision resistance: Finding two different inputs that produce the same hash is computationally infeasible — requiring more operations than atoms in the observable universe.
One-way function: The hash cannot be reverse-engineered to find the original content. Attackers cannot work backwards from a known hash to create a matching credential.
Avalanche effect: Changing a single character in the credential produces a completely different hash. There's no way to make small modifications that maintain the original hash.
To create a fake credential that passes blockchain verification, an attacker would need to:
Option 1 requires having the genuine credential, which defeats the purpose of fraud. Option 2 is mathematically impossible with current and foreseeable computing power.
AI excels at generating visually convincing content. But AI cannot:
The AI threat is real — but it's a visual threat. Blockchain verification operates in a different domain where AI capabilities don't apply.
Making your credentials AI-proof is simpler than you might expect.
Audit current credentials:
Identify high-value targets:
Define integration requirements:
Template creation: Work with TRUE to design credential templates that match your brand identity. Custom colours, logos, layouts, and animations — all secured by blockchain.
Workflow mapping: Define how credentials will be issued:
Verification experience: Design the verification experience for your credential viewers:
Connect your systems: TRUE offers multiple integration options:
Test thoroughly:
Communicate the change:
Monitor and optimise:
Most organisations complete the full transition in 2-4 weeks.
AI capabilities will continue advancing. Today's sophisticated AI will seem primitive within five years. Building AI-resistant credentials now protects against threats that haven't emerged yet.
Blockchain verification provides permanent protection because the security model is asymmetric:
Attacker burden: Must defeat cryptographic guarantees that improve over time (stronger hashes, more blockchain nodes, larger consensus requirements).
Defender burden: Maintain existing system. No additional investment required as AI advances.
As AI improves, blockchain doesn't need to keep up — it's already operating in a domain AI cannot reach.
Multi-chain verification: TRUE records credentials to multiple blockchains, ensuring redundancy even if one blockchain faces issues.
Algorithm evolution: As new cryptographic standards emerge, TRUE can incorporate them while maintaining backward compatibility with existing credentials.
Quantum readiness: Quantum computing poses theoretical future threats to some cryptographic systems. Blockchain networks are actively developing quantum-resistant algorithms. Credentials issued today will be upgradable to quantum-safe verification.
Organisations implementing AI-proof credentials gain advantages beyond fraud prevention:
Regulatory compliance: As regulators recognise AI fraud threats, blockchain verification may become required for certain credential types. Early adopters avoid scrambling to comply.
Competitive differentiation: Organisations offering verifiable credentials signal commitment to integrity. In competitive markets, this becomes a selling point.
Reduced verification burden: Instant blockchain verification eliminates the staff time currently spent responding to verification requests.
Marketing value: Credentials shared on LinkedIn carry verification capability, driving brand exposure when recipients share their achievements.
TRUE was built for this threat landscape. Every credential issued through TRUE carries blockchain-backed verification that AI cannot defeat.
TRUE writes credentials to four public blockchains:
This redundancy ensures credential verification even if any single blockchain experiences issues.
TRUE isn't theoretical. The platform has secured:
From government agencies (Bolagsverket) to leading medical universities (Karolinska Institutet) to professional associations (SSF, Great Place to Work), organisations trust TRUE for credentials that must withstand scrutiny.
AI has changed credential security forever. Visual security features that protected credentials for decades are now obsolete. Detection-based approaches cannot keep pace with AI generation capabilities.
Blockchain verification offers what AI cannot defeat: mathematical proof of authenticity that doesn't depend on visual inspection, human review, or database availability.
The organisations implementing AI-proof credentials today will be protected when — not if — AI-generated credential fraud becomes widespread. The organisations waiting will scramble to respond.
Protect your organisation's credentials from the new generation of AI-powered fraud.
Book a FREE Demo — See how blockchain verification defeats AI fakes.
Learn more:
→ How Blockchain Prevents AI-Generated Fake Certificates → Fake Certificate Verification Guide → Blockchain Certificate Verification → Pricing and Plans
Save time, increase traffic and insights and build trust, by upgrading to blockchain secured diplomas and course certificates, which are loved by recipients and always verifiably authentic.
Book a demoNot sure where to start? Let us help!

Trusted by leading organisations worldwide
